PII Compliance Services with The Scarlett Group
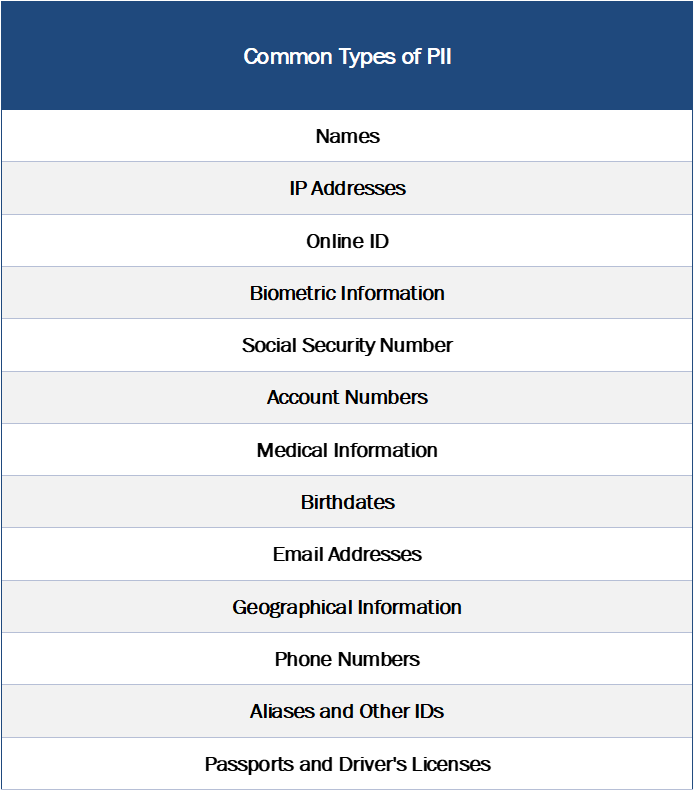
Organizations of all sizes and industries must comply with relevant legislation surrounding the protection and proper management of Personally Identifiable Information (PII). PII is defined as "data that can be used to identify specific individuals." Attackers and cybercriminals often target PII as the primary objective of their breaches, as this information is worth great financial and espionage value. The Scarlett Group offers complete managed PII protection and compliance services, enabling your organization to stop stressing over PII compliance.
PII and The Importance of Proper Compliance
Cybercriminals are fully aware of the value associated with PII that companies collect. Whether it be employee data, customer preferences, or even registration aliases - never underestimate the value of the information on your systems. Attackers will go to great lengths to compromise an organization with the goal of exfiltrating PII to use in future criminal activities. This PII can be sold, repurposed for Identify Theft, used for phishing attacks, and even ransomed. Don't be caught in the nightly news headlines as another victim of a costly PII breach. Work with our team to close the gaps in your network and protect the PII within your systems.
The Scarlett Group specializes in managed security and IT services. Our team will work with your existing IT and Cybersecurity staff to augment their capabilities, providing essential cybersecurity services and consultation. Our solutions align with the huge array of pre-defined cybersecurity compliance frameworks, providing the appropriate resources where necessary to accomplish complete compliance while remaining conscious of cost. No matter the size of the organization, we can affordably help close the security and IT gaps for the framework(s) that are relevant to your organization.
How We Help You Reach PII Compliance
Our PII Compliance program follows a series of tested principles with the goal of custom-developed PII protection and compliance objectives for your organization. We will execute a series of assessments and control evaluations designed to ensure that your organization is fully prepared and scoped for the PII protection recommendations that are relevant to your industry. We validate this compliance with automated solutions and manage or co-manage the security controls to protect your environment.
- Scope: We help your team determine the scale of the PII compliance situation within your organization in order to properly identify aspects such as required compliance level, devices and users affected, and more.
- Assess: A PII Compliance Gap Analysis is executed by experienced auditors, evaluating your organization's current protection and PII compliance gaps.
- Protect: After assessing your organization's PII gaps, our consultants will work with your team to identify the required cybersecurity services and governance solutions to achieve complete compliance and protection.
- Manage: PII Compliance Services are a managed and specialized affair. These PII protections and security controls require a dedicated cybersecurity team to ensure complete coverage. Our team will manage or co-manage cybersecurity controls, develop appropriate governance, and provide reporting on your organization's current compliance posture.
