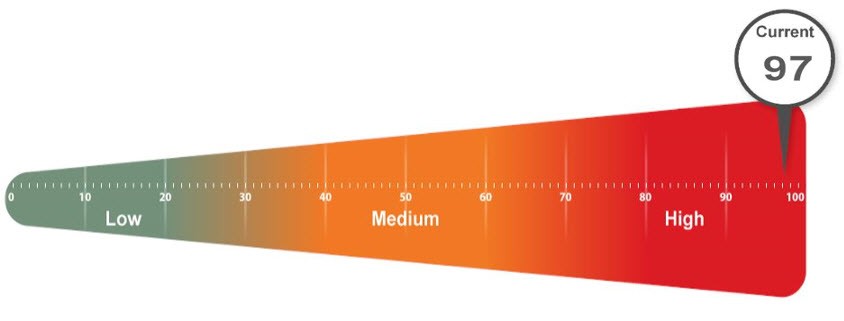
An unbiased Cybersecurity Assessment will either validate your current security posture or uncover risk reduction opportunities.
The Scarlett Group’s Assessment Team is led by ISACA Certified Auditors.
Cyber attacks against big organizations are well-publicized by the media, while attacks against small firms generate little attention. This can give small and medium-sized businesses a false sense of security. In a 2018 survey by the Ponemon Institute, 55% of small to medium-sized organizations responded that they had experienced a cyber crime in the previous year.
According to Forbes, “smaller enterprises find themselves more frequently targeted – sometimes as a conduit to their larger partners and customers.”
Third-Party Cybersecurity Audits and Assessments are a best practice and should be conducted every 18-24 months. We identify and quantify risks which enable you to make smarter decisions about your current technology, potential new investments and the optimal approach to enterprise risk management based on your business goals.
Preparation for Cyber Insurance Quotes and Policy Compliance
Unsurprisingly, more and more organizations are getting rejected for quotes regarding cyber insurance. Cyber insurance providers check for things like exposed services, proper policies, and third-party assessment frequency. Our cybersecurity assessments are the perfect solution for discovering the gaps within your organization's network that may be causing issues getting proper cyber coverage.
Our team deals with cyber insurance agencies on a daily basis. We know what they look for when quoting and we can provide assistance in identifying trouble areas that might stop your organization from even getting quoted coverage.
Our industry-leading holistic methodology includes:
Interviews:
We conduct interviews and focused dialog with executives and stakeholders. Our approach is flexible and considers your organization’s culture, IT environment, systems, business operations and priorities.
The state of the company’s cybersecurity:
- Key initiatives
- Desired goals and results
We conduct interviews and focused dialog with key department heads and process owners:
- What’s working, what’s not
- Ideas and concerns
We conduct interviews and focused dialog with internal and external IT teams:
- What working, what’s not
- Resource management
- Business alignment
- Ideas and concerns
Comprehensive IT Analysis:
We perform a comprehensive end-to-end infrastructure analysis. Our team employs software agents and centralized software performance monitoring tools to gather data for the client LAN and WAN. The IT infrastructure assessment consists of a thorough review of your IT infrastructure, business processes, policies and controls.
What you receive:
- Scorecard and model
- Onsite findings presentation by an ISACA Certified Auditor
- An Executive Summary for nontechnical stake holders
- Comprehensive, detailed findings delivered digitally and physically
- Interview results
- Recommendations and solution options